While vendor risk management (VRM) and third-party risk management (TPRM) are sometimes used interchangeably, they aren’t the same thing.
If you’re like most organizations, you outsource responsibilities to a third party to better serve customers, grow revenues, and cut costs. But bringing on third parties can also introduce a long list of risks that can do serious damage to an organization.
What is vendor risk management?
VRM refers to the process that organizations use to ensure that third-party products and services don’t lead to negative financial, reputational, regulatory, operational, and strategic consequences.
VRM is all about vetting partners, suppliers, and vendors to make sure they meet certain conditions. These conditions, along with the expectations for each party, are detailed within the vendor contract and include things like information security and regulatory compliance requirements. For example, you might specify how often a vendor audit needs to take place, or the password complexity requirements for anyone accessing your data.
“If a third-party or vendor violates a regulation, law, code of conduct, or internal organizational policy, you could pay the price.”
What is third-party risk management?
TPRM goes even deeper and includes every single third party, like partners, government agencies, your franchises, or charities in which you donate your time or money, as well as all your vendors. In this case, these organizations may require access to sensitive company data (e.g., to demonstrate compliance with government regulators), but you often have no ability to define who accesses it or how they use it—and there’s a good chance you can’t audit it.
TPRM often starts with VRM; it’s the foundation on which TPRM is built. Organizations will begin with a VRM program, and as they grow and mature, they’ll identify a need to address the specific and frequently disparate risks that a growing list of third parties present.
We talk more about TPRM in our eBook, Third-party risk management essentials.
The risks vendors pose to your organization
You’re putting a great deal of control into your vendors’ hands, which is why a continuous and automated third-party risk management solution is a good idea. Let’s look at three risks vendors can pose to your organization, along with some examples.
1. Regulatory risk
If a third-party or vendor violates a regulation, law, code of conduct, or internal organizational policy (either accidentally or knowingly), you could pay the price.
- Example: A healthcare company hires a developer to create an app that includes Protected Health Information (PHI) as The Health Insurance Portability and Accountability Act (HIPAA) defines it. The developer doesn’t ensure the app is HIPAA compliant, and the healthcare company gets fined.
2. Operational risk
This includes any third-party risk that could disrupt your operations, such as a data breach. On average, a data breach costs an organization $3.92 million.
- Example: A department store chain uses a customer service vendor to provide online chat support. The customer service vendor is hacked via malware, compromising credit card information and other personal data.
3. Reputational risk
As Warren Buffet said, “It takes 20 years to build a reputation, and five minutes to ruin it.” That damaged reputation can be in the news and on social media that quickly, too.
- Example: An electronics manufacturer outsources production to a factory that violates child labor laws, leading to fines and negative publicity.
Long-term VRM & TPRM
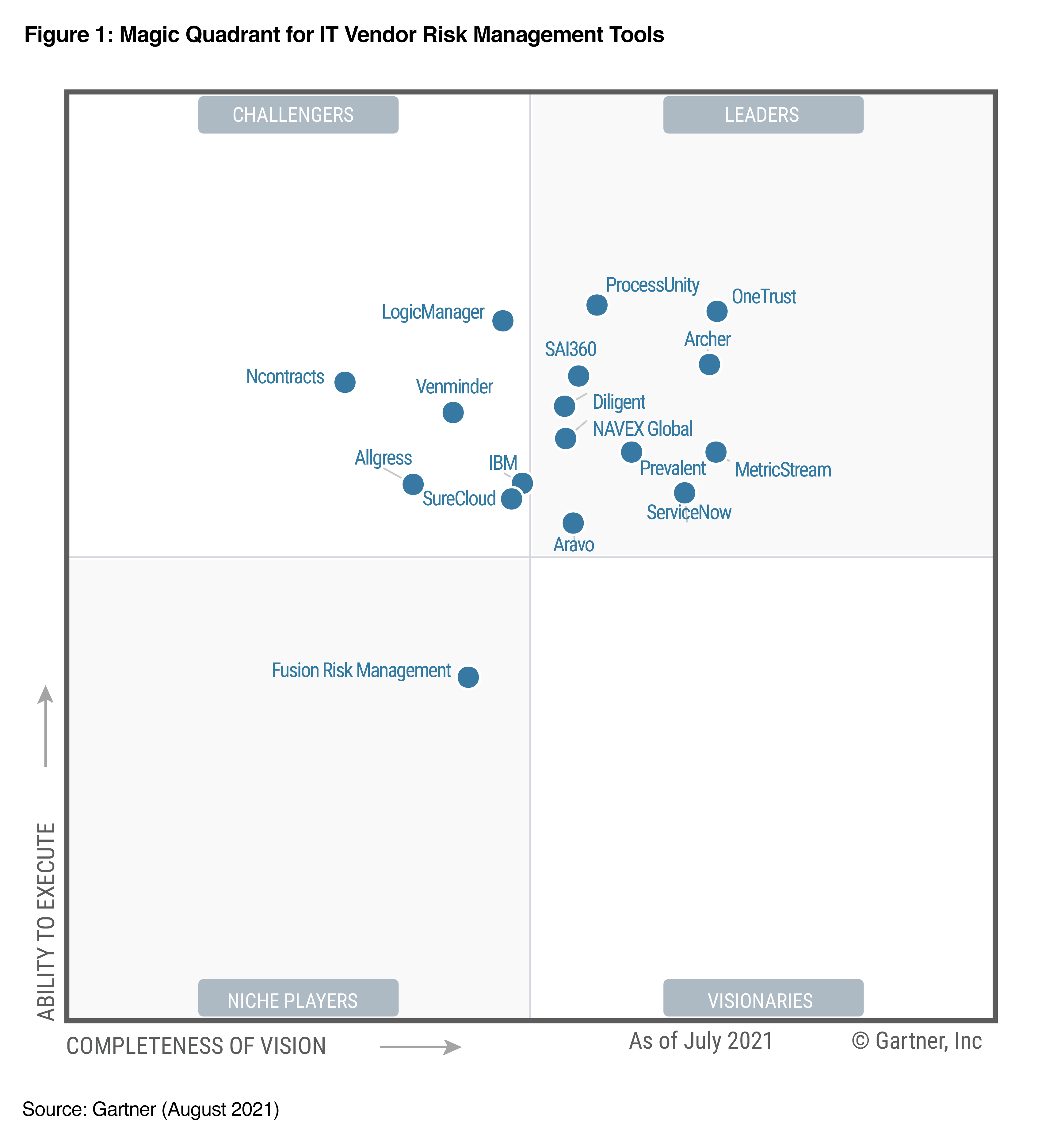
Just because a third party is compliant and careful today doesn’t mean that’s always going to be the case. Also, Gartner’s research shows that 71% of organizations report their third-party network contains more third parties than it did three years ago, with the same percentage reporting that network will grow even larger in the next three years.
Whether you take a VRM or TPRM focus, ongoing monitoring of your program is essential. It’s the only way you’ll be able to navigate an increasing number of risks and protect your customers and organization.
Learn about our third-party risk management capabilities.
eBook:
Third-party risk management essentials
This eBook explores the:
- Basics of third-party risk management.
- Difference between TPRM and vendor risk management.
- Process of picking a risk management framework that best fits your organization.