Cybersecurity management software
CyberBond allows you to effectively manage security operations (threats and vulnerabilities) and incident response functions (events and incidents) within a centralized cybersecurity management software.
Drive intelligent, risk-based decision making.
When working with multiple tools across an organization, it can be hard to sift through and prioritize the masses of threat, vulnerability, and security events data. CyberBond helps by consolidating disparate information and relationships across an organization’s tech stack and uses automation to drive intelligent decisions.
The cyber risk elements are processed through out-of-the-box or user-defined risk-based workflows, which automatically assign tasks, send notifications, and create escalations so you can prioritize your remediation efforts based on risk.
Why choose CyberBond?
Import data from multiple security tools, regardless of the format.
Business context driven cyber risk priortization and remediation workflow.
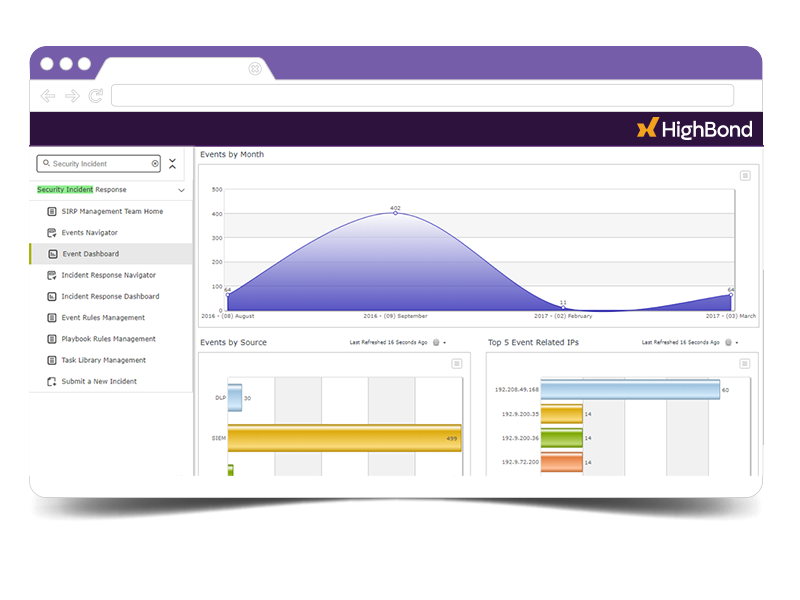
Automate reporting and triaging of security events.
Use data analytics to intelligently uncover compounded threats with large exposure.
Automated remediation tracking and escalation on missed target dates and risk levels.
Stay compliant with regulations while handling data breaches and data privacy incidents.
Centralized cyber-risk management platform
- Implement out-of-the-box connectors for 30+ well-known vulnerability scanners, SIEM, and other threat detection tools.
- Import data from any security tool that uses representational state transfer (REST) API.
- Automate and schedule data imports.
- Normalize scanning tool taxonomy imports for consistent risk reporting and workflow prioritization.
- Use the bidirectional API to integrate supporting systems like ticketing and case management.
Business context driven remediation & prioritization
- Dynamic rule-based triaging and prioritization of vulnerabilities and incidents.
- Custom rule definitions to include business context in prioritization of incidents and vulnerabilities.
- Capture compensating controls and risk acceptance.
- Automatically assign relevant tasks to appropriate individuals based on threat and vulnerability data.
- Record action plans, set target dates, and deliver timely reports.
- Blend assessment and vulnerability data for workflow escalations or downgrades.
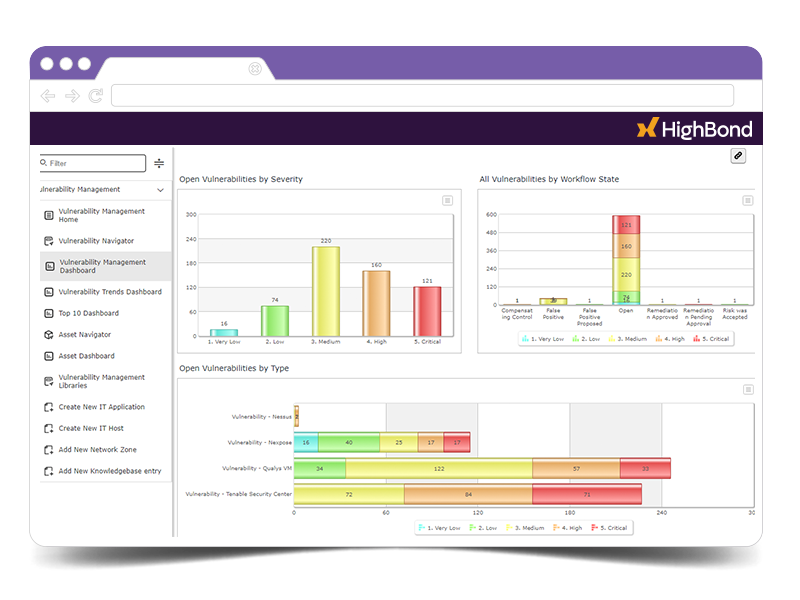
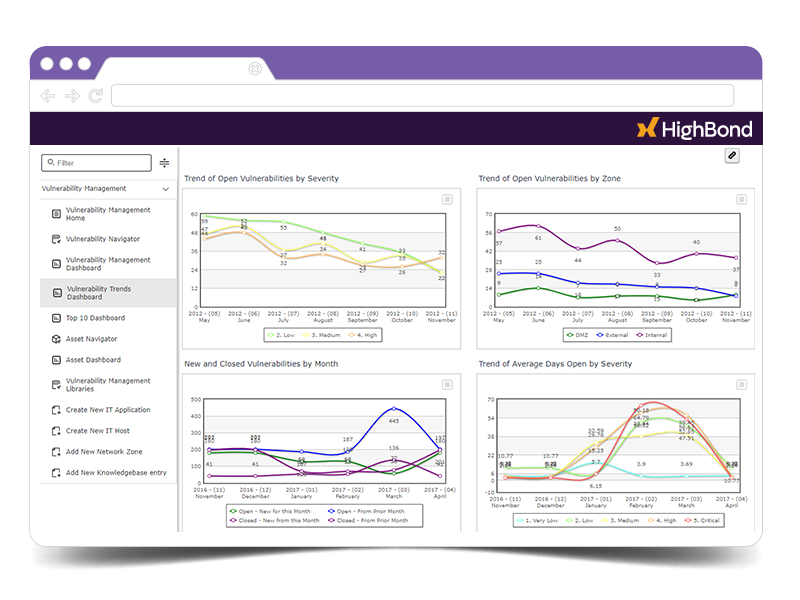
Holistic view of overall cyber risk posture
- Out of the box CISO-specific storyboards to share performance and status of cyber risk remediation metrics and trends.
- Quickly create reports and dashboards with a simple drag-and-drop interface.
- Highlight vulnerabilities in dashboards based on values like priority or severity.
- Generate impactful incident reports to make decisions at the executive level.
- Measure trends over time and automatically record and generate relevant metric data on a recurring schedule.
See how CyberBond can work for you.
Thanks for reaching out!
Your inquiry is now on its way to be processed and channeled to the best person to answer your questions. Once it lands in their inbox, they’ll be in touch.