IT departments play a significant role in ensuring HIPAA compliance. Learn what controls you can implement and how technology can help streamline your compliance.
What is HIPAA?
Enforced by the Department of Health & Human Services Office for Civil Rights, the Health Insurance Portability and Accountability Act is a regulation that protects the privacy of patients in healthcare organizations. It applies to many different groups—from hospitals and health plan providers, to clerks in doctors’ offices, and even the volunteers and trainees in these organizations.
HIPAA is focused on three basic issues: privacy, security, and administrative simplification.
HIPAA’s Privacy Rule determines how healthcare companies and professionals can use and disclose protected health information. They help make sure a patient’s protected health information is only shared with appropriate people in an appropriate way, and only if the patient gives permission.
The Security Rule is concerned with electronic protected health information (ePHI)—what HIPAA defines as any personally identifiable health information (e.g., blood type, doctor, room number) that’s digitally stored. The rule outlines specific expectations that organizations must meet to keep this information safe and make sure it’s used appropriately.
The Administrative Simplification section of HIPAA involves a national standard and series of standard codes that must be followed when identifying and diagnosing medical conditions and exchanging electronic information.
HIPAA compliance isn’t optional. All affected organizations need to have a plan in place for compliance.
What happens if organizations don’t comply?
The OCR conducts regular reviews and investigations to make sure healthcare organizations stay in compliance. If any violations are discovered, they can result in both civil and criminal penalties ranging from $100 to $250,000 per incident. Each record of data can count as a single incident.
For example, if a healthcare organization’s laptop containing 10,000 records is stolen, the fine could be $1 million or more. Healthcare professionals who knowingly disclose public health information can face even harsher penalties, like imprisonment for up to 10 years.
Anthem Inc., a licensee of Blue Cross and Blue Shield, is one organization that faced some serious penalties for non-compliance. In 2018, the company agreed to pay $16 million to the OCR for failing to implement measures that would detect hackers and prevent cyberattacks. As a result, the ePHI of 79 million people was exposed.
The data breach happened partially because Anthem:
- Didn’t conduct an enterprise-wide risk analysis
- Had insufficient procedures to regularly review information system activity
- Failed to identify and respond to suspected or known security incidents
- Overlooked implementing adequate minimum access controls to prevent the cyber attackers from accessing sensitive ePHI.
This event is considered to be the largest US health data breach in history. The OCR warns that the next round of audits for healthcare organizations in 2019 will be the harshest to date.
HIPAA can be quite vague in its expectations for protecting against cyberattacks, so to prepare for these audits, we recommend reading The American Health Information Management Association’s (AHIMA) 17 steps to create a plan for cybersecurity attacks.
So, what can be done to prevent data breaches in the future?
IT’s role in HIPAA compliance
When it comes to IT, the biggest pain is HIPAA’s Security Rule, which lays out expectations for handling and protecting ePHI. ePHI is at constant risk for being hacked, misplaced, or accessed by the wrong people (intentionally or unintentionally); IT departments are on the hook for making sure this information is protected so their organizations stay HIPAA compliant.
That means IT departments are in charge of:
- Maintaining the confidentiality, integrity, and availability of ePHI
- Protecting ePHI from hazards and threats
- Protecting ePHI from unauthorized use and disclosure
- Training employees to stay compliant with the rules.
To make sure these responsibilities are met, the IT department must put appropriate controls in place.
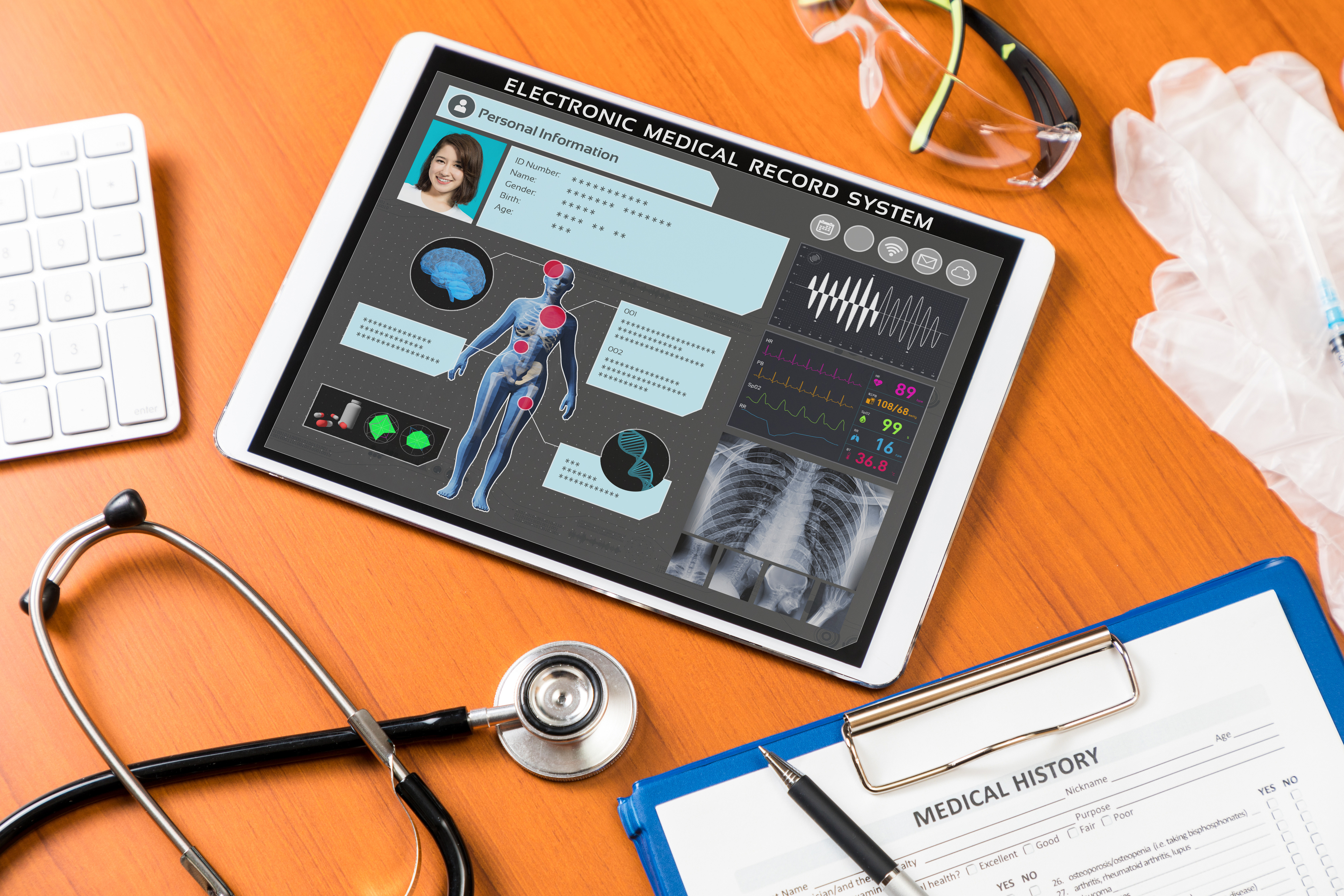
HIPAA requires the protection of digitally-stored health information.
What IT controls can be implemented for HIPAA compliance?
HIPAA has a long list of required and recommended security standards and safeguards to guide IT departments in meeting the Security Rule. A combination of administrative safeguards, physical safeguards, and technical safeguards is needed for compliance.
Administrative safeguards are controls that can be implemented through administrative efforts like conducting a risk assessment. This is actually the most foundational step towards HIPAA compliance. Check out this helpful HIPAA risk assessment template to get started.
Other examples include appointing a security officer, setting access levels, determining incident procedures, choosing a reporting contact, and setting up contingency plans for data emergencies.
Physical safeguards are measures taken to physically restrict access to places where ePHI is stored, like hospital computers or phones. Putting procedures in place to validate a worker’s facilities access is an example of a physical safeguard.
Technical safeguards are technology tactics that can help minimize access to ePHI, such as implementing automatic logoffs after periods of inactivity, or encrypting data wherever possible.
Technology solutions like ComplianceBond can be used as part of all of these safeguards.
How can I use technology to streamline HIPAA compliance?
Conducting risk assessments
Conducting an in-depth risk assessment is a first step towards preventing events like cyber attacks. By identifying all possible areas of risk, you can start to implement more specific controls. Governance, risk, and compliance (GRC) software makes it possible to conduct risk assessments and list all controls and responsible employees within the software. If a control is neglected, it will notify the right individuals to fix the issue immediately. If, for example, a security officer isn’t appointed, your risk level increases and you’re able to take corrective action.
Testing controls
To help prevent instances of employees having wrongful access, GRC software can be used for assigning access levels to specific user profiles and conducting tests to find outliers that might have additional, unauthorized data access. This helps IT adjust access rights proactively, and in half the time, rather than taking the risk of waiting for an incident to occur before taking corrective action.
Enforcing security training
Employee security training is a HIPAA requirement. To make sure your employees understand their own roles in HIPAA compliance, schedule security training regularly for the following occasions:
- During new-hire onboarding
- When there are changes to the regulation
- Periodically as check-ins.
Technology can be used both to administer training and check that it’s being done. Some software can send out surveys that ask employees to confirm they have completed the required training. You can also see how employees are performing on security training and make a note of those who require additional support.
IT departments play a significant role in ensuring HIPAA compliance. Recent data breaches confirm just how serious non-compliance penalties can be. To make sure your organization is HIPAA compliant, take the time to review HIPAA’s Security Rule and implement the required and recommended administrative, physical, and technical controls. Technology solutions are essential in each step of HIPAA compliance to identify major risks and compliance weaknesses, and speed up corrective action. It is worth exploring GRC software options as well as additional resources to help guide you towards effective compliance.
eBook
Better practices for compliance management
You’ll learn:
- 5 common compliance management challenges
- How to create a high-performance compliance management process
- How to transform your compliance program
- How technology can improve compliance
- What technology you need for a high-performance program.